Claude Code Source Code Leak 2026: What Anthropic Exposed in npm Source Map Error
What Anthropic Exposed
in the npm Packaging Error — v2.1.88On March 31, 2026, Anthropic shipped Claude Code v2.1.88 to npm with a 59.8 MB cli.js.map source map file, exposing the full 512,000+ lines of TypeScript source across 1,900 files. The leak revealed 44 unreleased feature flags, internal telemetry, encryption logic, and multi-agent orchestration code. No customer data was compromised, but the incident marks Anthropic's second major leak in weeks.
What Happened: The npm Source Map Mishap
Anthropic's official @anthropic-ai/claude-code package for version 2.1.88 contained a production artifact never intended for public release: the unobfuscated cli.js.map file. Source maps are debugging files that map minified JavaScript back to original TypeScript source.
Security researcher Chaofan Shou discovered the exposure within hours. Community mirrors quickly appeared on GitHub, making the full codebase permanently available. Anthropic removed the source map and older package versions, describing it as a "release packaging issue caused by human error."

// Anthropic accidentally published Claude Code's source code — The Media Copilot, March 2026
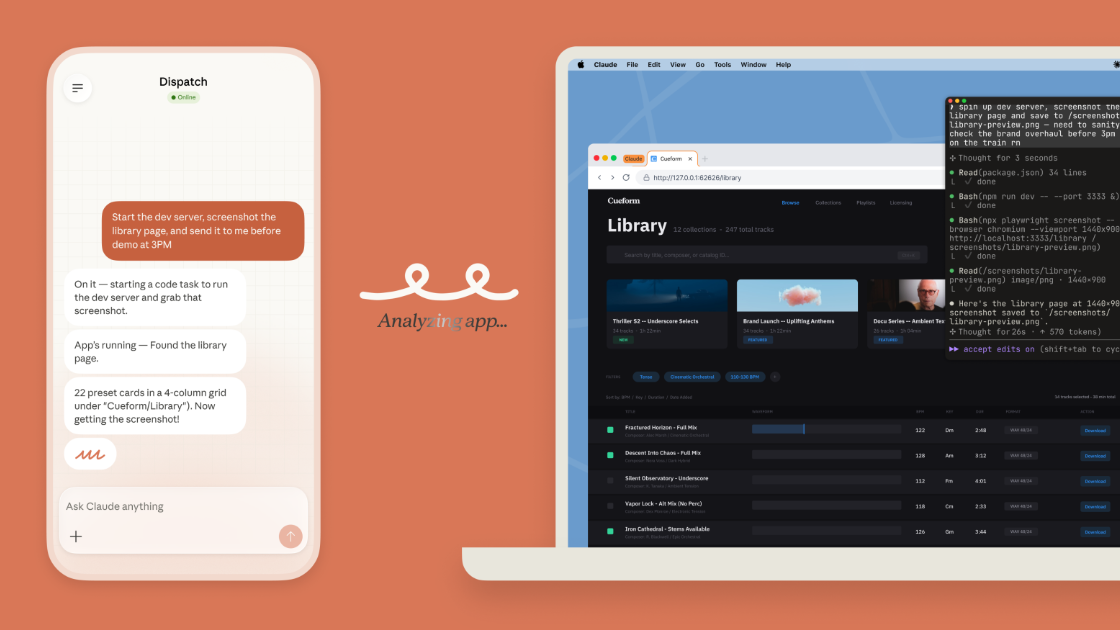
Claude Code: The Agentic CLI Interface
Claude Code is Anthropic's terminal-first agentic tool that lets developers plan, execute, debug, and ship code using natural language — making the source exposure particularly significant for security researchers.
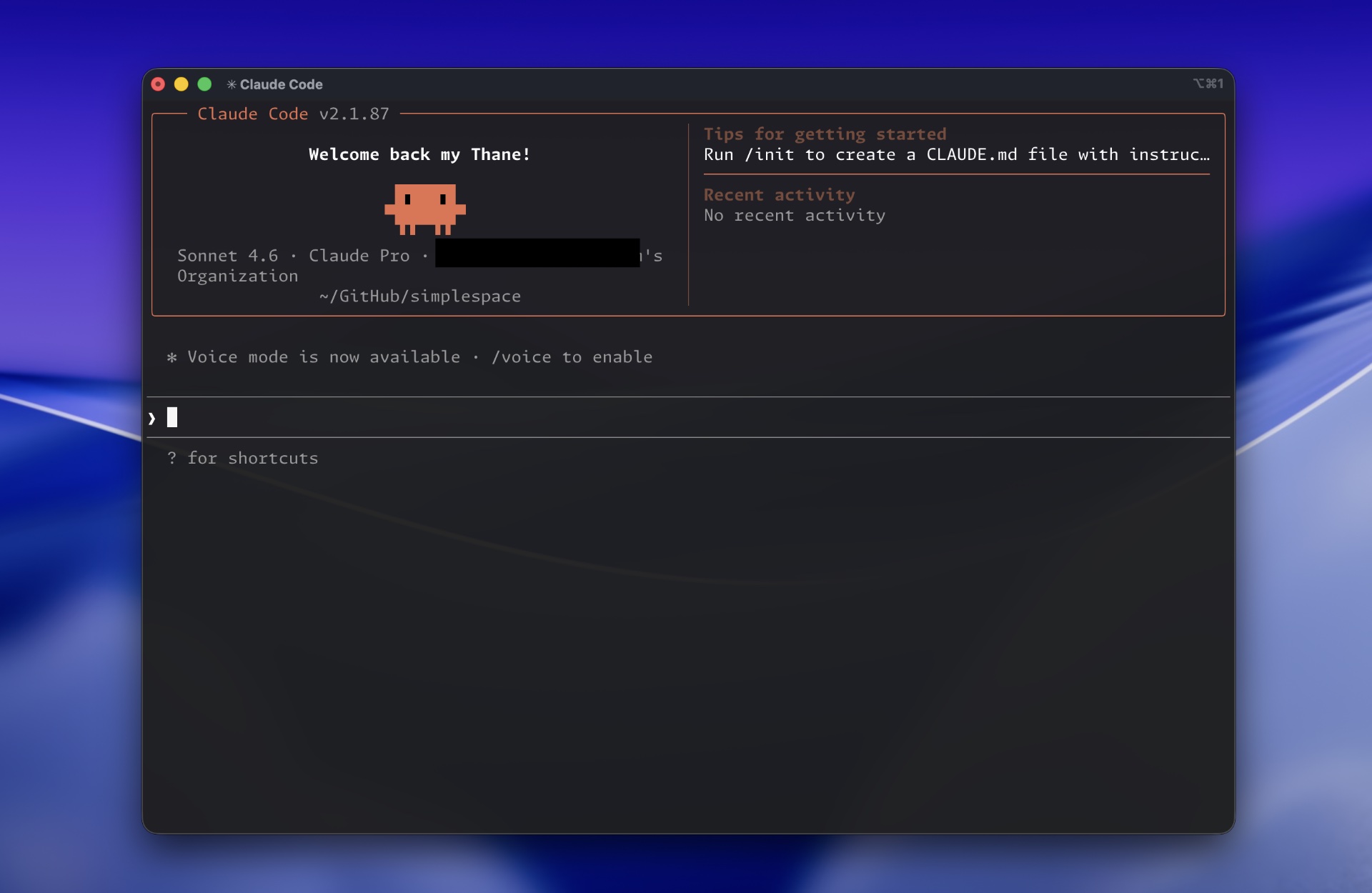
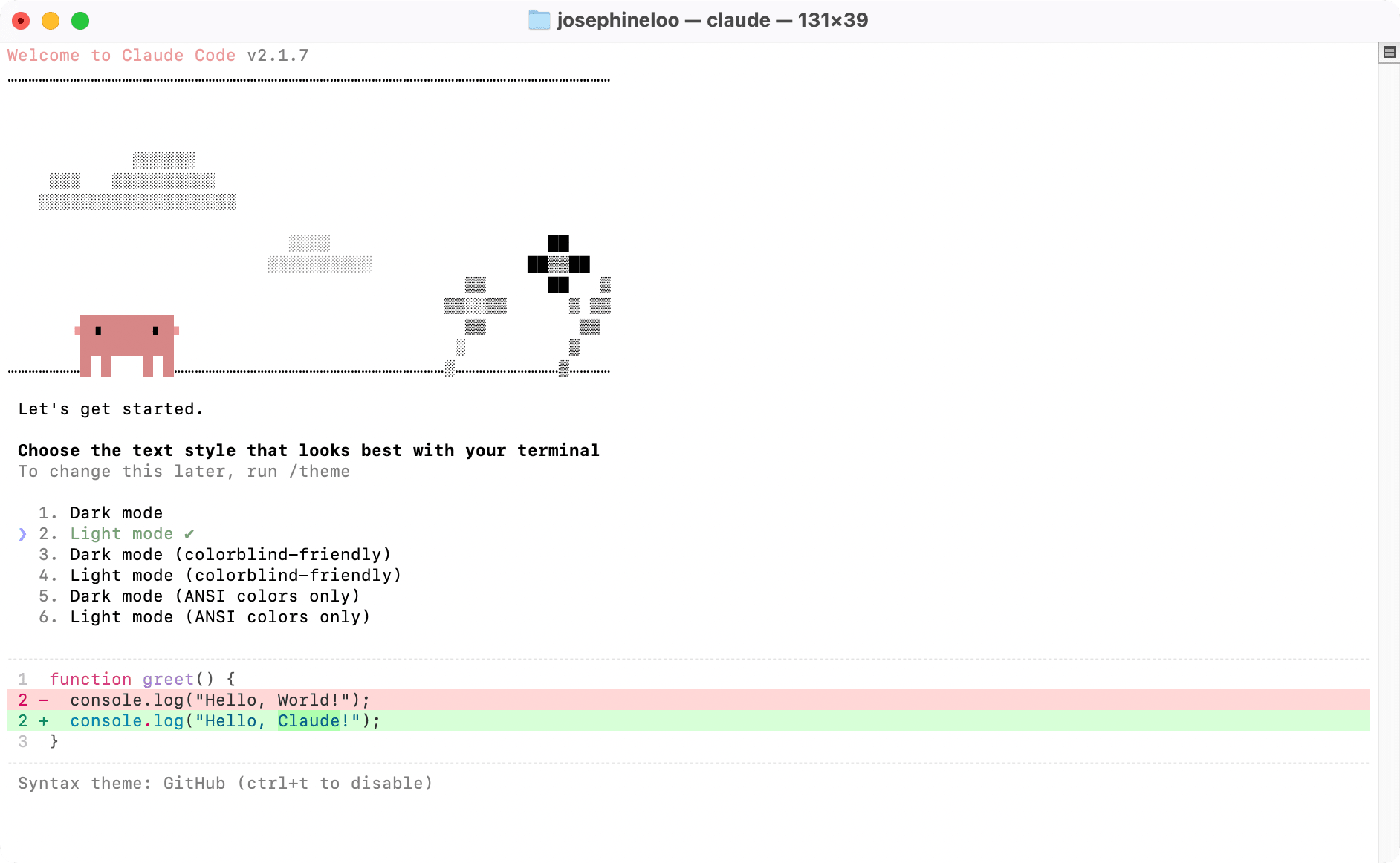
// Claude Code in action: terminal interface, agentic workflow, and installation overview
Exactly What Was Exposed: 44 Unreleased Feature Flags
- KAIROS — a persistent background daemon (always-on agent) that maintains long-term memory and proactively suggests improvements.
- Buddy — a Tamagotchi-style virtual companion that gamifies code maintenance tasks.
- Voice Mode, Proactive Agent flags, and detailed multi-agent orchestration logic.
- Complete system prompts and internal safety policies.

// Anthropic accidentally leaked Claude Code's source — The Internet Is Keeping It Forever (Decrypt via Yahoo)
Why This Leak Matters: Three Hard Numbers
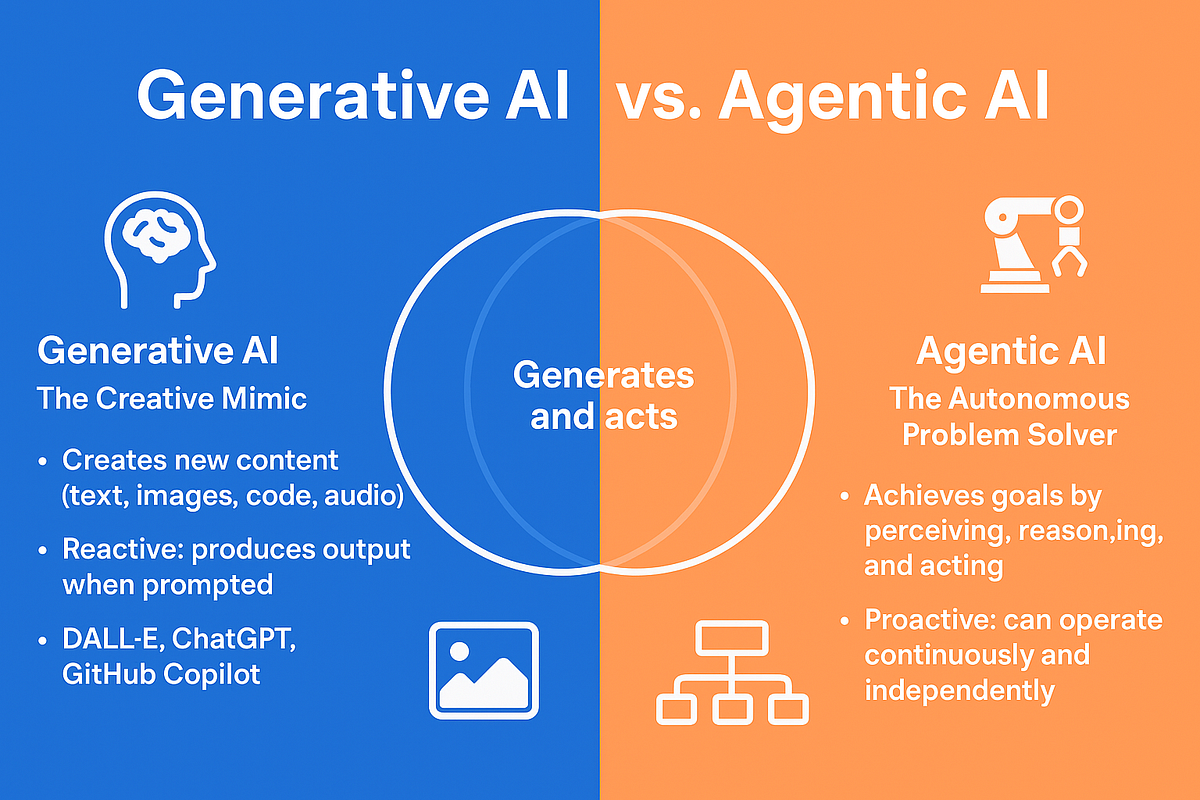
// Generative AI vs Agentic AI: understanding the attack surface difference (Medium)
Expert Perspective
Exposing surrounding agentic tooling — CLI logic, orchestration, memory systems — lowers the bar for reverse-engineering guardrails and building adversarial variants. Even without model weights, the blueprint for how Claude Code interacts with models can now be studied or attacked at scale. This accelerates both legitimate open-source forks and sophisticated jailbreak techniques.
Implications for Developers & Enterprises
The leak makes reverse-engineering far easier and underscores that agentic AI tools are becoming the new attack surface. Enterprises relying solely on one vendor's CLI now face single-vendor concentration risk. The smart strategy is multi-model routing through a unified API layer that automatically falls back between providers while preserving the agentic experience.


// Agentic AI workflows and enterprise security implications
FAQ
No. The leak contained only internal source code — no credentials, user prompts, or conversation history were compromised.
Yes, the official package has been cleaned. However, the mirrored source remains public, so scrutinize future releases carefully for build artifacts.
Scan npm pipelines for source-map inclusion, implement automated secret scanning, and consider a unified AI API gateway that abstracts vendor-specific CLIs.
It accelerates adoption. The real differentiator is no longer the CLI itself, but the stability and security of the underlying API access layer.
The Claude Code source leak is a wake-up call. For developers building agentic applications, the clearest lesson is: never bet the farm on a single vendor's CLI or API. A unified, battle-tested integration platform with intelligent routing and automatic fallback is now essential for production-grade AI development.


 Log in
Log in